 I have added one new item to the SIGINT Summaries page. The Summaries include downloadable copies of leaked Communications Security Establishment (CSE) documents, along with summary, publication, and original source information.1 CSE is Canada’s foreign signals intelligence agency and has operated since the Second World War.
I have added one new item to the SIGINT Summaries page. The Summaries include downloadable copies of leaked Communications Security Establishment (CSE) documents, along with summary, publication, and original source information.1 CSE is Canada’s foreign signals intelligence agency and has operated since the Second World War.
Documents were often produced by CSE’s closest partners which, collectively, form the ‘Five Eyes’ intelligence network. This network includes the CSE, the National Security Agency (NSA), the Government Communications Headquarters (GCHQ), Australian Signals Directorate (ASD),2 and Government Communications Security Bureau (GCSB)).
All of the documents are available for download from this website. Though I am hosting the documents they were all first published by another party. The new documents and their summaries are listed below. The full list of documents and their summary information is available on the Canadian SIGINT Summaries page.
The new contribution comes from documents released by CBC and covers how Five Eyes intelligence analysts correlated telephony and mobile Internet communications information. For the first time I have noted, in the summary block, all of the codenames that were mentioned in the redacted document.
Synergising Network Analysis Tradecraft: Network Tradecraft Advancement Team (NTAT)
Summary: This slide deck showcases some of the activities, and successes, of the Network Tradecraft Advancement Team (NTAT). The slides focus on how to develop and document tradecraft which is used to correlate telephony and Internet data. Two separate workshops are discussed, one in 2011 and another in 2012. Workshop outcomes included identifying potentially converged data (between telephony and Internet data) as well as geolocating mobile phone application servers. A common mobile gateway identification analytic was adopted by three agencies, including DSD. NTAT had also adopted the CRAFTY SHACK tradecraft documentation system over the courses of these workshops.
In an experiment, codenamed IRRITANT HORN, analysts explored whether they could identify connections between a potentially ‘revolutionary’ country and mobile applications servers. They successfully correlated connections with application servers which opened up the potential to conduct Man in the Middle attacks or effect operations towards the mobile devices, as well as the potential to harvest data in transit and at rest from the devices. In the profiling of mobile applications servers it appears that EONBLUE was used to collect information about a company named Poynt; that company’s application was being used by Blackberry users, and the servers profiled were located in Calgary, Alberta (Canada).
The agencies successfully found vulnerabilities in UCWeb, which was found to leak IMSI, MSISDN, IMEI, and other device characteristics. These vulnerabilities were used to discover a target and it was determined that the vulnerabilities might let a SIGINT agency serve malware to the target. A ‘microplugin’ for XKeyscore was developed so that analysts could quickly surface UCWeb-related SIGINT material. (NOTE: The Citizen Lab analyzed later versions of UCWeb and found vulnerabilities that were subsequently patched by the company. For more, see: “A Chatty Squirrel: Privacy and Security Issues with UC Browser.”)
Document Published: May 21, 2015
Document Dated: 2012 or later
Document Length: 52 pages (slides plus notes)
Associated Article: Spy agencies target mobile phones, app stores to implant spyware
Download Document: Synergising Network Analysis Tradecraft: Network Tradecraft Advancement Team (NTAT)
Codenames mentioned: ATLAS, ATHENA, BLAZING SADDLES, CRAFTY SHACK, DANAUS, EONBLUE, FRETTING YETI, HYPERION, IRRITANT HORN, MASTERSHAKE, PEITHO, PLINK, SCORPIOFORE
Footnotes
 In our recent report, “The Governance of Telecommunications Surveillance: How Opaque and Unaccountable Practices and Policies Threaten Canadians,” we discussed how the Communications Security Establishment (CSE) developed and deployed a sensor network within domestic and foreign telecommunications networks. While our report highlighted some of the concerns linked to this EONBLUE sensor network, including the dangers of secretly extending government surveillance capacity without any public debate about the extensions, as well as how EONBLUE or other CSE programs programs collect information about Canadians’ communications, we did not engage in a comparison of how Canada and its closest allies monitor domestic network traffic. This post briefly describes the EONBLUE sensor program, what may be equivalent domestic programs in the United States, and the questions that emerge from contrasting what we know about the Canadian and American sensor networks.
In our recent report, “The Governance of Telecommunications Surveillance: How Opaque and Unaccountable Practices and Policies Threaten Canadians,” we discussed how the Communications Security Establishment (CSE) developed and deployed a sensor network within domestic and foreign telecommunications networks. While our report highlighted some of the concerns linked to this EONBLUE sensor network, including the dangers of secretly extending government surveillance capacity without any public debate about the extensions, as well as how EONBLUE or other CSE programs programs collect information about Canadians’ communications, we did not engage in a comparison of how Canada and its closest allies monitor domestic network traffic. This post briefly describes the EONBLUE sensor program, what may be equivalent domestic programs in the United States, and the questions that emerge from contrasting what we know about the Canadian and American sensor networks.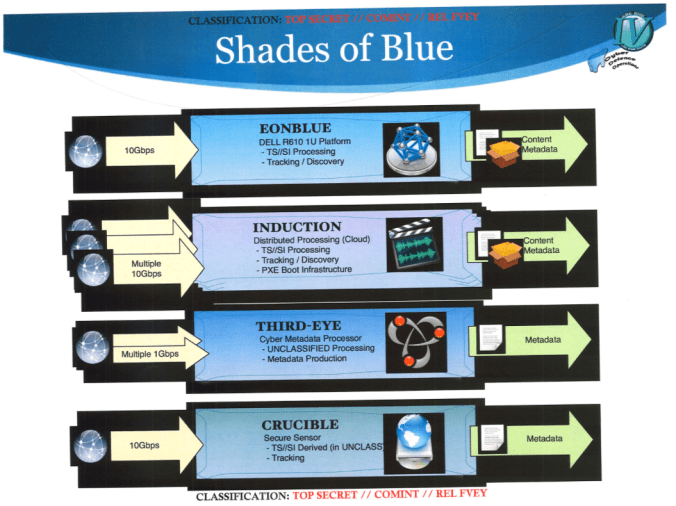
 I have added one new item to the SIGINT Summaries page. The Summaries include downloadable copies of leaked Communications Security Establishment (CSE) documents, along with summary, publication, and original source information.
I have added one new item to the SIGINT Summaries page. The Summaries include downloadable copies of leaked Communications Security Establishment (CSE) documents, along with summary, publication, and original source information. Journalists with access to leaked documents have reported on the partnerships and activities undertaken by Canada’s foreign signals intelligence (SIGINT) agency, the Communications Security Establishment (CSE), since October 2013. As a result of their stories we know that the Canadian government hosts collection facilities in its diplomatic outposts for American SIGINT operations, has co-ordinated with the NSA to monitor for threats to international summits that took place in Canada, and shares a cooperative relationship with the National Security Agency (NSA) to protect North America from foreign threats. CSE, itself, was found to be conducting signals intelligence and development operations against the Brazilian government, running experiments using domestically collected metadata to track Canadians’ devices, and automating both the discovery of vulnerable computer devices on the Internet for later exploitation and identifying network administrators’ Internet traffic.
Journalists with access to leaked documents have reported on the partnerships and activities undertaken by Canada’s foreign signals intelligence (SIGINT) agency, the Communications Security Establishment (CSE), since October 2013. As a result of their stories we know that the Canadian government hosts collection facilities in its diplomatic outposts for American SIGINT operations, has co-ordinated with the NSA to monitor for threats to international summits that took place in Canada, and shares a cooperative relationship with the National Security Agency (NSA) to protect North America from foreign threats. CSE, itself, was found to be conducting signals intelligence and development operations against the Brazilian government, running experiments using domestically collected metadata to track Canadians’ devices, and automating both the discovery of vulnerable computer devices on the Internet for later exploitation and identifying network administrators’ Internet traffic.

