In our recent report, “The Governance of Telecommunications Surveillance: How Opaque and Unaccountable Practices and Policies Threaten Canadians,” we discussed how the Communications Security Establishment (CSE) developed and deployed a sensor network within domestic and foreign telecommunications networks. While our report highlighted some of the concerns linked to this EONBLUE sensor network, including the dangers of secretly extending government surveillance capacity without any public debate about the extensions, as well as how EONBLUE or other CSE programs programs collect information about Canadians’ communications, we did not engage in a comparison of how Canada and its closest allies monitor domestic network traffic. This post briefly describes the EONBLUE sensor program, what may be equivalent domestic programs in the United States, and the questions that emerge from contrasting what we know about the Canadian and American sensor networks.
In our recent report, “The Governance of Telecommunications Surveillance: How Opaque and Unaccountable Practices and Policies Threaten Canadians,” we discussed how the Communications Security Establishment (CSE) developed and deployed a sensor network within domestic and foreign telecommunications networks. While our report highlighted some of the concerns linked to this EONBLUE sensor network, including the dangers of secretly extending government surveillance capacity without any public debate about the extensions, as well as how EONBLUE or other CSE programs programs collect information about Canadians’ communications, we did not engage in a comparison of how Canada and its closest allies monitor domestic network traffic. This post briefly describes the EONBLUE sensor program, what may be equivalent domestic programs in the United States, and the questions that emerge from contrasting what we know about the Canadian and American sensor networks.
What is EONBLUE?
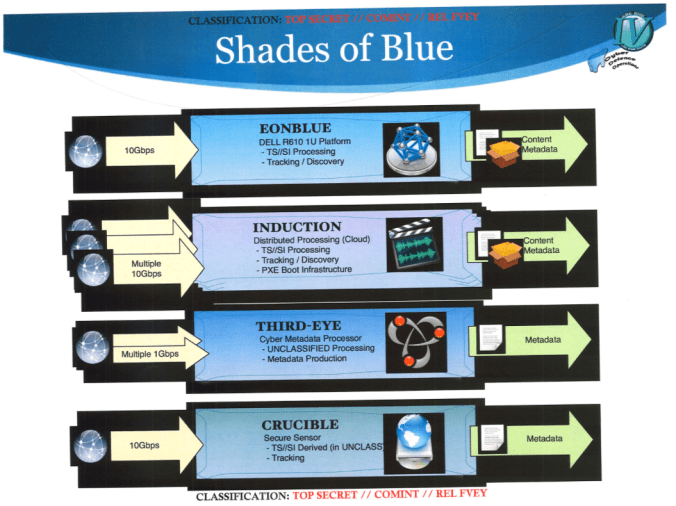
EONBLUE was developed and deployed by the CSE. The CSE is Canada’s premier signals intelligence agency. The EONBLUE sensor network “is a passive SIGINT system that was used to collect ‘full-take’ data, as well as conduct signature and anomaly based detections on network traffic.” Prior Snowden documents showcased plans to integrate EONBLUE into government networks; the network has already been integrated into private companies’ networks. Figure one outlines the different ‘shades of blue’, or variations of the EONBLUE sensors: